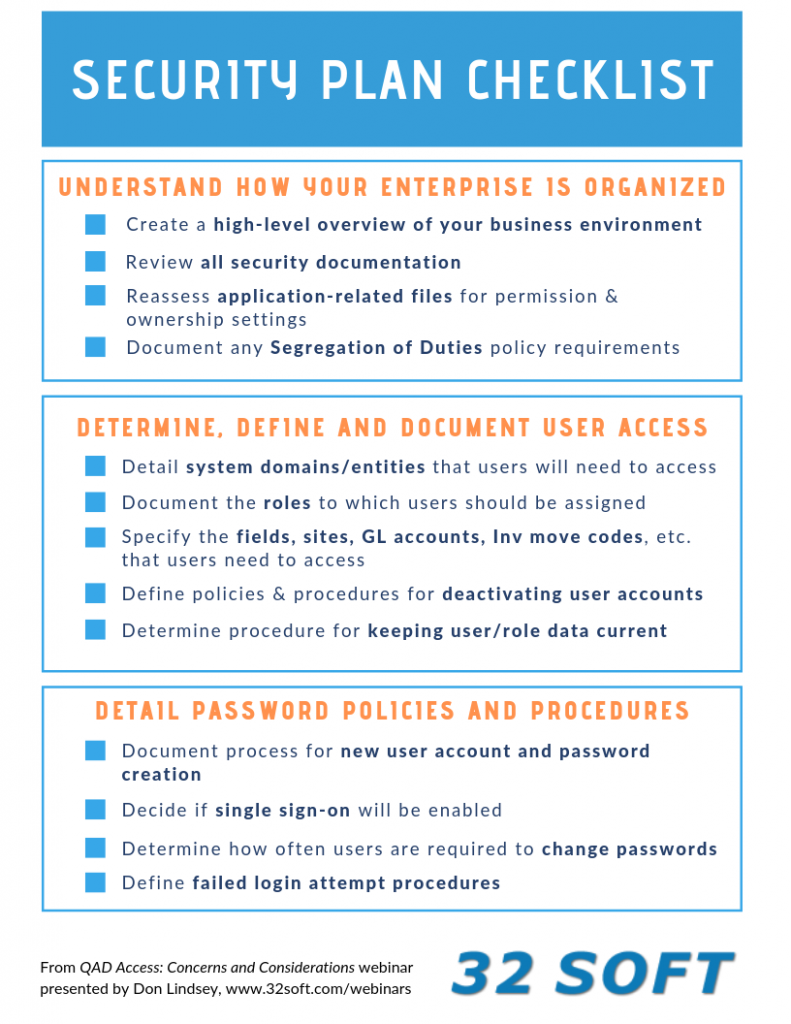
QAD Access Security Plan Checklist
 In a recent webinar, QAD Access: Concerns and Considerations, presenter Don Lindsey included a to-do list of tasks that should be considered before you embark on setting up your permissions and roles in QAD.
In a recent webinar, QAD Access: Concerns and Considerations, presenter Don Lindsey included a to-do list of tasks that should be considered before you embark on setting up your permissions and roles in QAD.
You’ll find a downloadable pdf of this graphic here: Security Plan Checklist
Don’s checklist includes:
Review, Determine and Understand How Your Enterprise is Organized
- Create a high-level overview of your business environment, including information about multiple sites, multiple domains, licenses, etc.
- Review all security documentation, including .Net, email security, the board of directors’ requirements, etc.
- Reassess all application-related files to determine appropriate permission & ownership settings
- Document any Segregation of Duties policy requirements
Determine, Define and Document User Access
- Detail the system domains/entities that users will need to access
- Document the roles to which users should be assigned
- Specify the Fields, Sites, GL Accounts, Inv Move Codes, etc. that users need to access
- Define policies and procedures for deactivating old user accounts
- Determine policies and procedures to assure user/role information is kept current
Detail Password Policies and Procedures
- Document the process for new user account and password creation
- Decide if single sign-on will be enabled
- Determine how often users are required to change passwords
- Define failed login attempt procedures
To learn more about Roles and Permissions, watch our webinars on the subject here:
QAD Access: Concerns and Considerations
Implications of QAD Roles and Responsibilities
Improve QAD menu security maintenance, audit and analysis with Data Loader




